How does the bitcoin source code define its 21 million cap?
Many of bitcoin’s staunchest critics have expressed doubt about its 21 million cap, but perhaps the most mindless criticism relates…
,Over the weekend, Jeremy Welch from Casa gave a talk at Baltic Honeybadger 2019 highlighting the threats posed by rogue web extensions in browsers. It’s important to educate users on potential threats and how to defend against them. We applaud drawing attention to this problem but we are disappointed with how this threat was presented. Our team was not able to make it to Riga this year to view the presentation in person, and we feel it is important to provide our perspective.
The talk demoed a browser extension attack, but there are many other types of man-in-the-middle attacks that should worry bitcoiners. Keyloggers, rootkits, copy/paste viruses, simjacking, and malicious mobile apps are just as scary and easy to execute, although more difficult to demo in a live talk. Such exploits can compromise personal information and payment details for any web service, including Amazon, Google, Facebook, banks and health insurers, as well as monitor web traffic and even record from the microphone and camera.
These attacks can be built for any website, but Casa chose to demo a custom browser extension targeting Unchained Capital’s application. A similar exploit could be crafted for amazon.com, coinbase.com, or Casa’s own website and mobile app. By highlighting Unchained’s website, Casa disingenuously framed a general security problem with browsers as a particular problem with a competitor’s website, which ultimately cheapens our discourse and confuses customers.
Companies rely on users to avoid malicious software. Less careful users are difficult to protect, so it is valuable to educate them about how to mitigate threats. We wish Casa had not stopped at repeating known threats and had instead offered more practical solutions than completely abandoning web browsers. We link to some basic resources at the end of this article that any user can follow to protect against the kind of attack Casa demonstrated, which apply generally to all web browsing. Our role is not to scare users but to educate and empower them. The ultimate defense against the attack presented is external address verification.
Bitcoin delivers greater security and privacy, so bitcoiners rightly worry that they have more to lose than the average computer user when interacting online with third parties. We have previously written about the trade-off between privacy and security on our platform.
Bitcoiners can use cryptographic methods to verify, rather than trust, the people and companies with whom they transact. Most companies in bitcoin do not allow customers to control their own private keys and ignore these valuable verification methods. Unchained Capital and Casa are among the few companies in the world who encourage users to own their own keys and verify addresses externally.
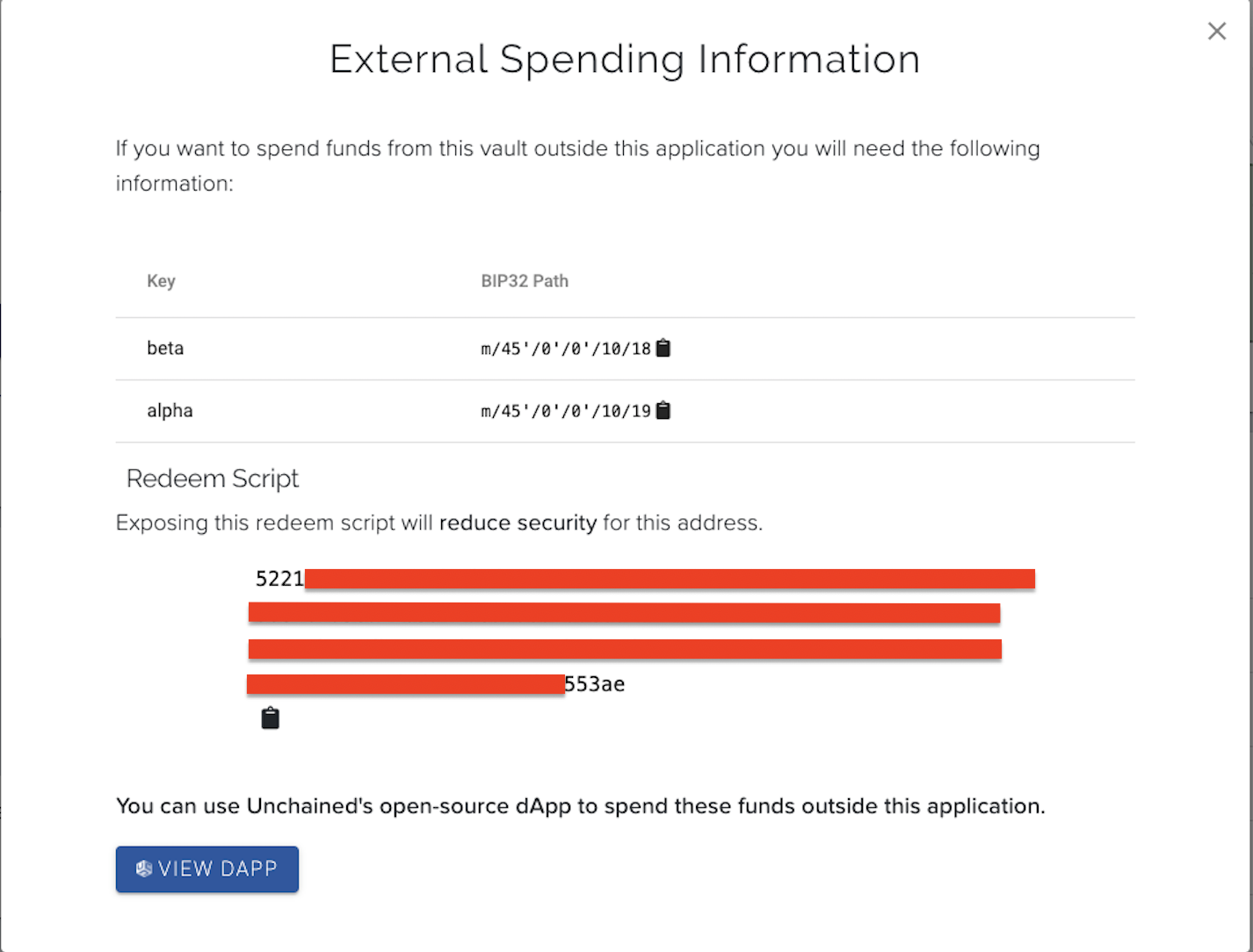
Casa used their custom-built web extension to demo changing an address displayed by Unchained’s website, but they neglected to show the features of our product which mitigate against exactly these kinds of man-in-the-middle attacks. In particular, we give customers the information they need (redeem scripts and BIP32 paths to public keys) to verify that all addresses displayed by our platform are ultimately controlled by their keys. This feature addresses the kinds of threats created by malicious web extensions, and has been part of our product since 2018. We have been actively working on improvements to this feature and open source tools to make address verification more accessible to less-technical users.
Casa failed to demo or mention this crucial security feature of our platform in their talk.
Transitioning to ubiquitous multisig and collaborative custody is important for bitcoin’s long-term security. We know Casa believes this as well. For this reason, we respect Casa as a company and as a competitor despite taking issue with their presentation at Baltic Honeybadger. Their excellent team and products elevate multisig standards for all bitcoiners, and we hope to work with them to drive the industry toward more secure multisig standards.
If you have any questions or would like to talk more about how Unchained Capital’s security model works, please drop us a line at hello@unchained.com
Computing devices such as laptops and phones have many layers to secure: physical, hardware, firmware, operating system, networks, applications & browsers. At each layer, greater security usually means less convenience. A user’s threat model should consider how security & convenience are balanced at each layer. Some users may benefit from a physical lock more than an encrypted hard drive.
There is much more to say on this subject but here are some simple steps you can follow to greatly increase your defenses:
Many of bitcoin’s staunchest critics have expressed doubt about its 21 million cap, but perhaps the most mindless criticism relates…
Ted Stevenot, Stephen HallWhen Satoshi Nakamoto created bitcoin, he established in its code a fixed number of bitcoin that will ever exist. Since…
Ted StevenotOriginally published in Parker’s dedicated Gradually, Then Suddenly publication. Bitcoin is often described as a hedge, or more specifically, a…
Parker Lewis